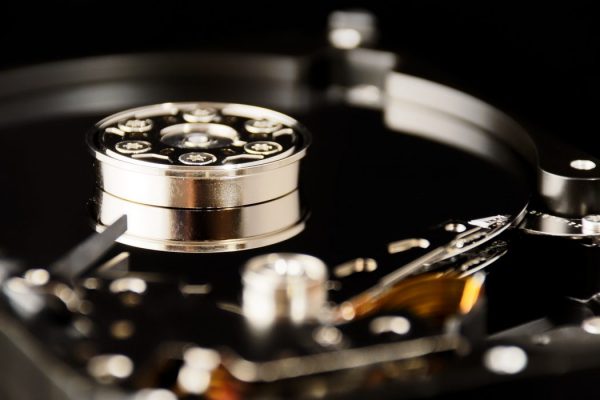
It is important to remember that when we drag a computer file to the trash, it is not really deleted. The data still exists on the hard drive. It is only the index file that is removed which includes the file’s location on the hard drive. When a file is “deleted,” the index entry for that file is eliminated so your computer can no longer find it. The problem is that the actual file itself still exists. It has not been destroyed.
The growth of cloud computing and its acceptance by companies of all sizes has caused a shift in how businesses use and save their electronic files. These companies are turning over human resource files, personal health information, financial records, payroll documents, and other confidential data to third-party data centers who they entrust with storing, monitoring, and maintaining this data. Any breach of security can have critical implications for both the company who owns the data and the data center...
When thinking about a computer network, we often focus on uptime/availability. Is the network up and running? Will you be able to access your data on-demand? Although uptime is very important, it is only one half of the computing equation. The other half, and some might argue the more important half, is the speed at which data travels. How quickly and efficiently your data can travel across the network from one point to another is just as important as if the network is available. Although discussions of uptime may receive the most attention on technology news and corporate websites, low...
Technology products and services have traditionally been sold using a bulleted list of features. Product features and price were nearly the same across competing products and the main differentiating factor was how comfortable the customer felt with the salesperson. But times have changed. Today’s sales process has matured beyond selling a bulleted list of features to selling a complete solution which enables technology and business savvy customers to solve their problems and achieve their business goals.
The U.S. Health Insurance Portability and Accountability Act requires specific security controls for businesses that store or process protected health information online. MULTACOM Data centers meet all of the necessary requirements for HIPAA on the data center/service provider side. For more information about and assistance to achieve, certify, and maintain HIPAA compliance for your environment, please contact our sales team.