Is Your Critical Company Data Really Gone When It’s Deleted? What You Can Do to Make Sure It Is.
What Actually Happens When You Delete A File?
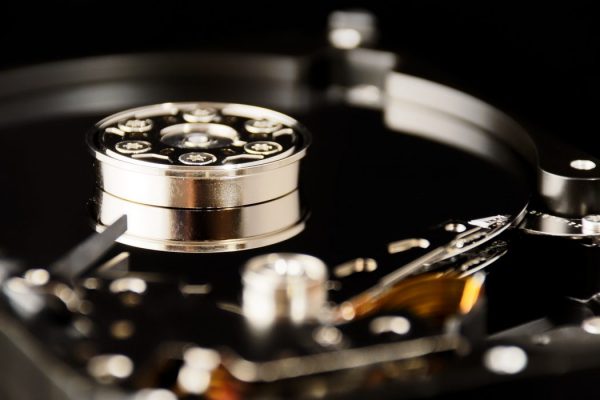
It is important to remember that when we drag a computer file to the trash, it is not really deleted. The data still exists on the hard drive. It is only the index file that is removed which includes the file’s location on the hard drive. When a file is “deleted,” the index entry for that file is eliminated so your computer can no longer find it. The problem is that the actual file itself still exists. It has not been destroyed.
This is good news if you decide that you need to get it back for some reason but not good news if you are trying to prevent criminals from getting their hands on confidential personal and company information. By using readily accessible recovery software, retrieving the data is straightforward.
It is one thing if your servers are stored in your office or your company’s personal data center where your in-house IT staff manages all of your company’s hardware themselves. They have physical control over the hard drives and most likely follow specific policies and procedures on how to dispose of company data to guard against hackers stealing information.
But, what happens when your company’s dedicated servers reside in a third-party data center and they are managed and maintained by a company that may not have your security interests as their top priority?
Where Does Your Data Go?
It is difficult to know what really happens with your information when the data center servers they were stored on are no longer needed because they have reached end of life or you have migrated to another provider.
The hard drives could be returned to the manufacture, reused by another client, or sold on an auction site like eBay. Whatever the final outcome, your data still resides on the device and could be accessed by the manufacturer or, more importantly, by cyber-criminals. They can use the same retrieval software as your IT department would to exploit the supposedly deleted data.
Corporate financial information, personal client data, and proprietary records are some of the most critical assets of your organization. It is not only essential to protect them while they are actively being used by you, but also when it is decided they are no longer be important. They may not be important to your business any longer, but they may be important to a competitor or cyber-criminal.
It is especially critical for you to ensure your data center provider has policies in place to permanently destroy all of the information on the hard drive. How does your provider eliminate their clients’ data? Can they assure you that when they say your data has been destroyed, it actually has? What physical measures do they have in place?
How MULTACOM Does It Differently.
At MULTACOM we take the protection of our clients’ data very seriously. We work directly with each client to provide custom security measures and put them in place from the moment you become a client to the time that a server has reached the end of its useful life. Our security measures are rare in the industry and include:
- Drives Returned to The Client: Some MULTACOM clients who want to maintain physical control of the servers ask that used drives are shipped to their office monthly or after they have reached end of life. This is quite an uncommon service which most data centers do not provide but one that we feel is important to safeguard our clients’ data.
- Hardware is Physically Destroyed: Most other dedicated server providers return equipment to the manufacturer or whomever the device was leased from. The hard drive can then be sold on the secondary market to other service providers, wholesalers, or anyone looking for previously used equipment, including hackers. At MULTACOM, our standard policy on how to handle end of life hardware is to physically destroy it. Our drives are damaged beyond repair, so the hardware is actually destroyed and data is completely inaccessible.
The widespread use of third-party data centers for the creation, handling, storage and maintenance of corporate data, whether it be harmless emails, important financial records, or highly confidential competitive intelligence, has added a new element of risk to data security. How do you protect the data that is out of your control? The key is to select a provider for whom a client’s data security is as important to them as it is to you and one that goes to above and beyond industry standard measures to protect you.
Contact MULTACOM today to learn more about how we handle your sensitive company data.
